The Importance Of Strong Passwords: Protect Yourself Online!
In today’s interconnected world, strong passwords are your first line of defence against cyber threats. However, many people still underestimate how easily weak passwords can be cracked. In this post, I aim to demonstrate why robust passwords matter, demonstrate the vulnerabilities of simple passwords, and offer practical tips for securing your online accounts.
Why Strong Passwords Matter
Malicious Actors employ various methods to breach systems, and weak passwords make their job significantly easier. Data breaches from companies like LinkedIn and RockYou have shown how devastating it can be when passwords are stored or used insecurely. Weak or reused passwords put not only a single account at risk but potentially your entire digital identity.
The Basics: How Passwords Are Stored
When you create a password, secure systems store a hashed version rather than the actual password. Hashing converts your password into a fixed-length string of characters. A good hash function ensures that even a minor change in the password produces a vastly different output.
However, some companies have used insecure hashing algorithms like MD5 or SHA-1, both of which are now considered vulnerable. Worse yet, storing passwords in plaintext or using outdated encryption has led to numerous high-profile data breaches.
Demonstration: How Simple Passwords Are Cracked
To understand the risks of weak passwords, I’d like to provide a simple demonstration using a tool called Hashcat. Similar results can also be achieved with a tool named John the Ripper:
- The Setup: Let’s pretend for a moment that we have breached the security
of a website where you hold an account. We have accessed the website’s database
of secure passwords and retrieved the hash value associated with your account.
The hashed password is —
f2c0e856a8b9dc060296c6e3889a3c93. This hash corresponds to an MD5-encrypted password. - The Wordlist: We will use a popular list of words from the data breach of the
company “RockYou”, this list contains
14344392cleartext passwords obtained from the breach. Hashcat will use this list to hash each word and compares it against the hash we “obtained” above. - The Result: Within seconds, the password
classof08is cracked.
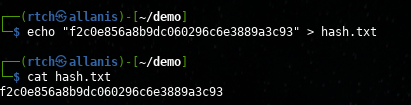
In the image below, we echo the output of the hash string and use the redirect >
symbol to store it in a file named hash.txt. We then cat the image to show that
the text was inserted into the file correctly.
This next command will invoke hashcat along with the supplied parameters. The table below describes each part of this command.
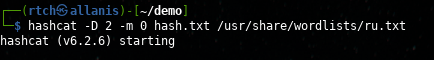
| Command Parameter | Description |
|---|---|
hashcat |
runs the hashcat program |
-D 2 |
Specifies the type of device to use [1:CPU, 2:GPU, 3:BOTH] |
-m 0 |
Specifies the hash type (0 = MD5) |
hash.txt |
The hash(s) we want to crack |
/usr/share/wordlists/ru.txt |
The location of the wordlist to compare against |
Lastly, the below image shows the final output of the Hashcat command. I have pointed out some key elements within the image.
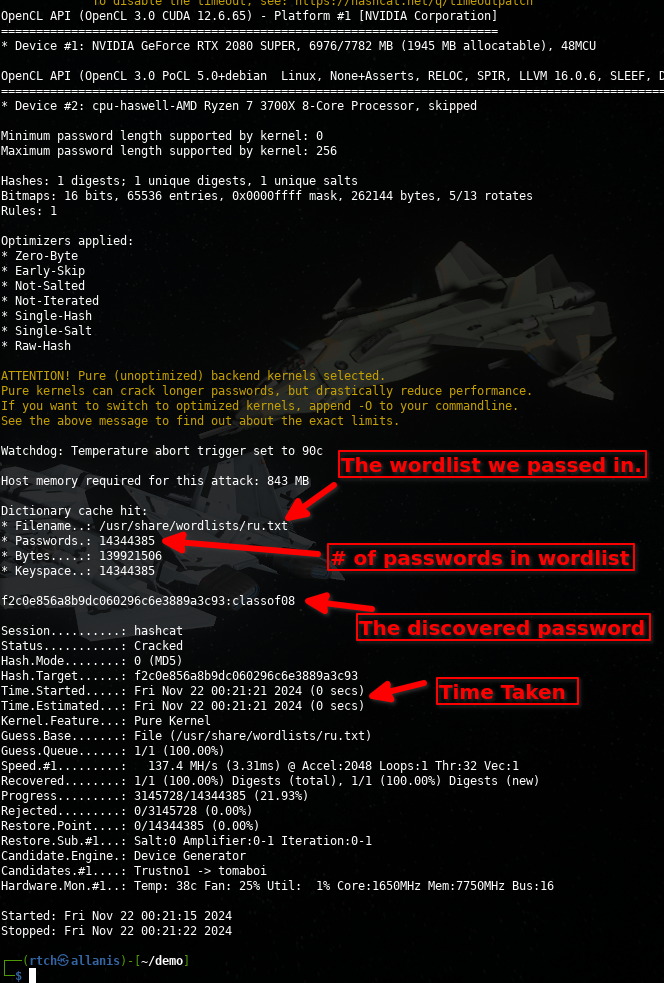
This simple demonstration highlights how common passwords are trivial to crack using readily available tools and public wordlists.
Advanced Attacks: Rainbow Tables and GPUs
Malicious actors often use rainbow tables to crack hashes. These pre-computed tables allow attackers to match hashed passwords to plaintext ones rapidly. While salts (random values added to passwords before hashing) can mitigate rainbow table attacks, they are only effective if implemented correctly.
Additionally, modern GPUs can process billions of hash computations per second, making brute-force attacks against weak hashing algorithms remarkably fast.
How to Protect Yourself
Protecting your digital accounts starts with strong and practical password practices. Based on NIST’s 2024 guidelines, here are some actionable tips to help keep your accounts secure:
-
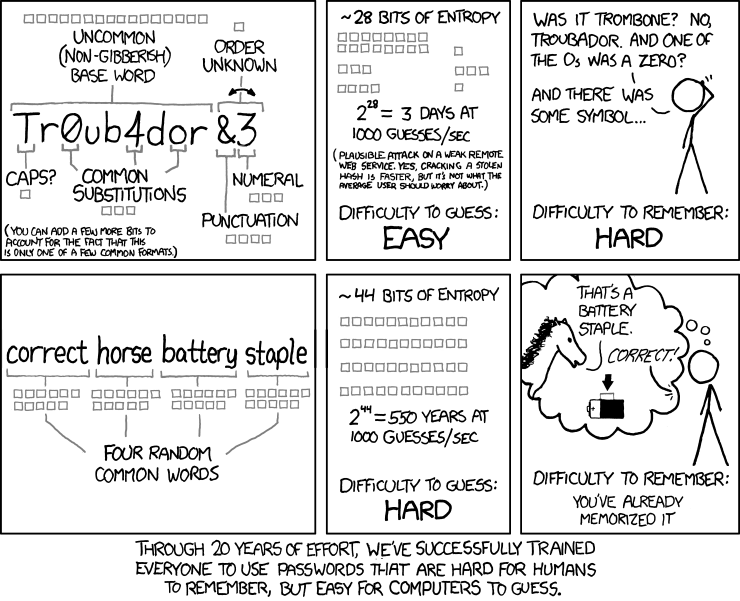
Make It Long: Password length is more critical than complexity. Aim for at least 12 characters or longer. Use passphrases — a series of words that are easy to remember but hard to guess (e.g., “CorrectHorseBatteryStaple”).
-
Avoid Complexity Overload: You don’t need to overload passwords with unnecessary complexity, such as mandatory symbols or upper/lowercase mixing, unless required. Focus on length and memorability instead.
-
Use a Password Blocklist: Ensure your passwords are not on a list of commonly used or previously breached passwords. Passwords like “Password1!” or “12345678” are easy targets for attackers.
-
Enable Spaces in Passphrases: Use spaces to create memorable yet strong passphrases, such as “my dog loves cheese pizza”. Spaces make passphrases easier to type and remember while increasing their strength.
-
Don’t Reuse Passwords: Every account should have its own unique password. If one account is breached, reuse could compromise all linked accounts.
-
Enable Two-Factor Authentication (2FA): Always activate 2FA where available. This adds an extra layer of security, requiring something you know (password) and something you have (e.g., a code from an app or SMS).
-
Avoid Writing Passwords Down: If you must record a password, ensure it is stored securely, such as in a password manager. Avoid unsafe methods like sticky notes or unsecured text files.
-
Update Weak or Old Passwords: Regularly review and update your passwords, especially those created before you adopted stronger practices.
-
Be Cautious with Public Inputs: Avoid entering passwords on public or shared devices, as they may be compromised with malware or keyloggers.
-
Protect Your Recovery and MFA Method: Your email, authentication application and password manager are critical password recovery tools. Always ensure these passwords are different from your other logins. It is also recommended that you never login to your email unless you explicitly typed your email providers URL into the browser manually.
Long, memorable passphrases are the cornerstone of strong password security. Avoid relying on excessive complexity, reuse, or outdated practices. Combined with 2FA, these tips ensure robust protection for your accounts while maintaining usability.
The Takeaway
Strong passwords are more than a suggestion—they’re a necessity. The sophistication of password cracking tools makes it imperative to adopt robust password practices. By understanding the risks and implementing the tips above, you can significantly enhance your digital security and protect your sensitive information.
Remember, a password is like a lock on your digital life. Make sure it’s strong enough to keep intruders out.